Comprehensive Phishing Detection Platform Architecture
Comprehensive phishing detection platform with desktop agents, backend infrastructure, AI analysis, and SOC integration. Learn about PhishMonger's architecture.
The Challenge
Security teams need comprehensive visibility into phishing threats across endpoints, email, and browser activity. Traditional security tools operate in silos, making it difficult to correlate threats and respond effectively.
Our Solution
PhishMonger's unified platform architecture provides end-to-end visibility from endpoint agents through backend analysis to SOC dashboards, enabling security teams to detect, analyze, and respond to threats in real-time.
The Outcome
Security teams achieve unified threat visibility, faster incident response, improved detection coverage, and comprehensive reporting for executive and compliance requirements.
Architecture Overview
PhishMonger's architecture enables comprehensive threat detection through a combination of local agents, centralized backend processing, and AI-powered analysis.
Desktop Agents
Cross-platform agents for Windows, macOS, and Linux
Backend Platform
Scalable API and database infrastructure
AI Analysis
Advanced pattern recognition and threat intelligence
SOC Dashboard
Real-time visibility and incident response
Pattern Learning
Continuous improvement through local and backend sync
Simulation Server
Safe training environment for security teams
Platform Components
Desktop Agents
Cross-platform desktop agents monitor browser and email activity in real-time. Agents run on Windows, macOS, and Linux, providing local-first analysis with zero-trust architecture. Process detection, active window tracking, and event capture enable comprehensive threat monitoring.
- Cross-platform support (Windows, macOS, Linux)
- Real-time browser and email monitoring
- Local-first analysis for privacy
- Process and window focus detection
- Event-driven architecture (no polling)
Backend Platform
Scalable backend infrastructure processes events from agents, provides API endpoints for SOC integration, and manages pattern learning synchronization. Built with enterprise-grade security and multi-tenant support.
- RESTful API for SOC integration
- WebSocket support for real-time updates
- Multi-tenant architecture
- Pattern learning synchronization
- Audit logging and compliance
Pattern Learning Engine
Continuous learning engine that improves detection capabilities through local pattern recognition and backend synchronization. Patterns are learned locally first, then synchronized with the backend for organization-wide intelligence.
- Local-first pattern learning
- Backend synchronization
- Deterministic pattern merging
- Source tracking (local vs backend)
- Daily pattern updates
Simulation Server
Safe, sandboxed phishing simulation environment enables security training without external network access. Campaign generators create realistic attack scenarios, and detection coverage mapping validates security readiness.
- Sandboxed simulation environment
- No external network access
- Automated campaign generation
- Attack chain scoring
- MITRE-based reporting
SOC & Analyst Experience
Comprehensive dashboard and tools for security operations centers and analysts. Real-time threat visibility, incident response workflows, and forensic analysis capabilities enable effective security operations.
- Real-time threat dashboard
- Incident response workflows
- Forensic analysis tools
- Event timeline visualization
- Integration with SIEM systems
Executive Reporting
Board-level reporting and executive dashboards provide high-level visibility into security posture, threat trends, and risk metrics. Compliance-ready reports support audit and regulatory requirements.
- Executive dashboards
- Risk metrics and trends
- Compliance reporting
- Board-level summaries
- Custom report generation
Platform Screenshots
Explore the PhishMonger platform through real screenshots from the dashboard
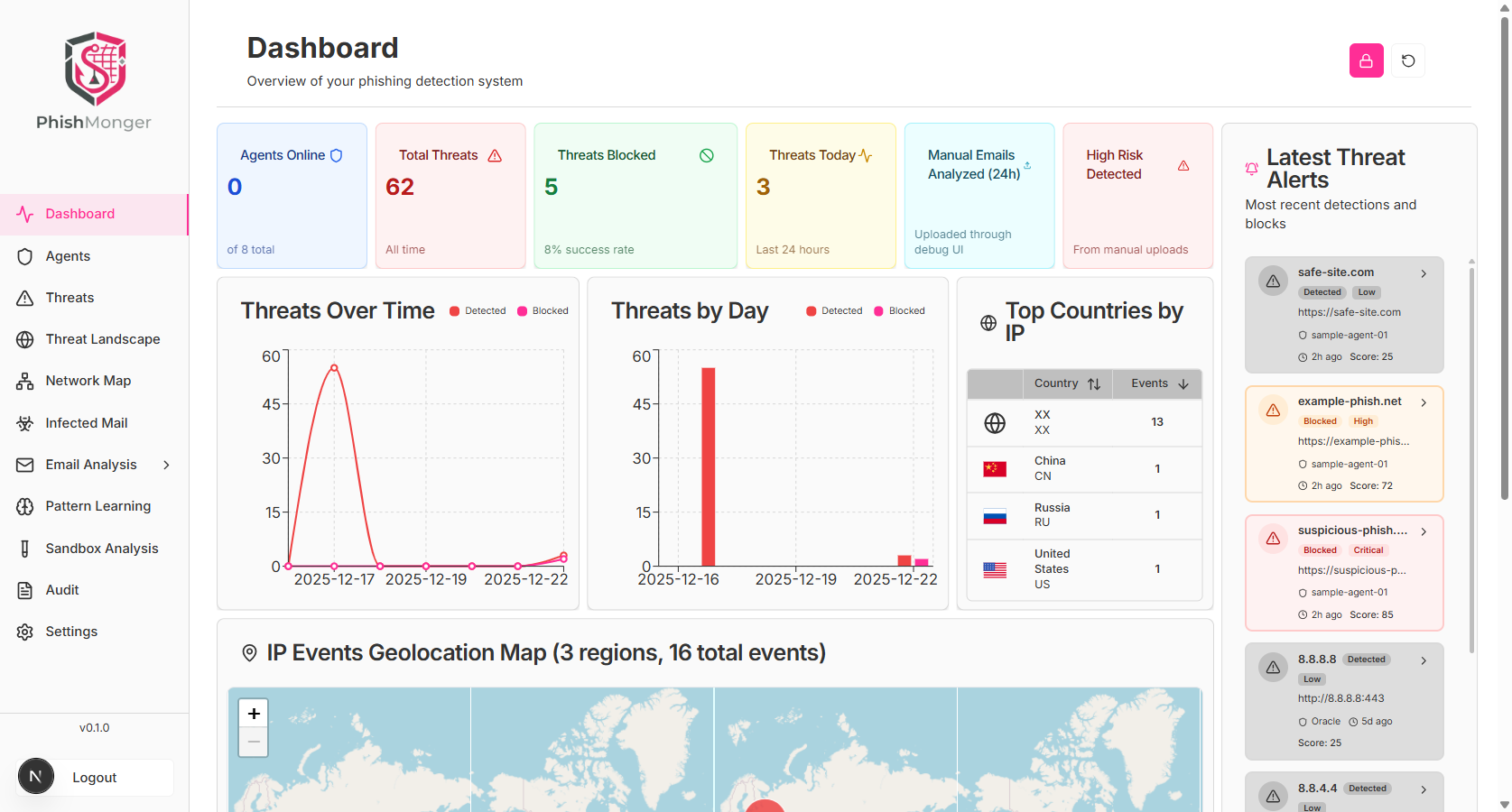
Main Dashboard

Threats View

Agent Management

MITRE ATT&CK Matrix

Pattern Learning

Executive Reports
Integration Points
PhishMonger integrates seamlessly with your existing security infrastructure
Wazuh SIEM
Forward events to Wazuh for centralized security monitoring
Email Systems
Integrate with email security gateways and clients
SOC Tools
API integration with existing SOC workflows and tools
Threat Intelligence
Share anonymized threat intelligence with security community
Why Trust PhishMonger
Enterprise Architecture
Scalable Infrastructure
Multi-Tenant Support
API-First Design